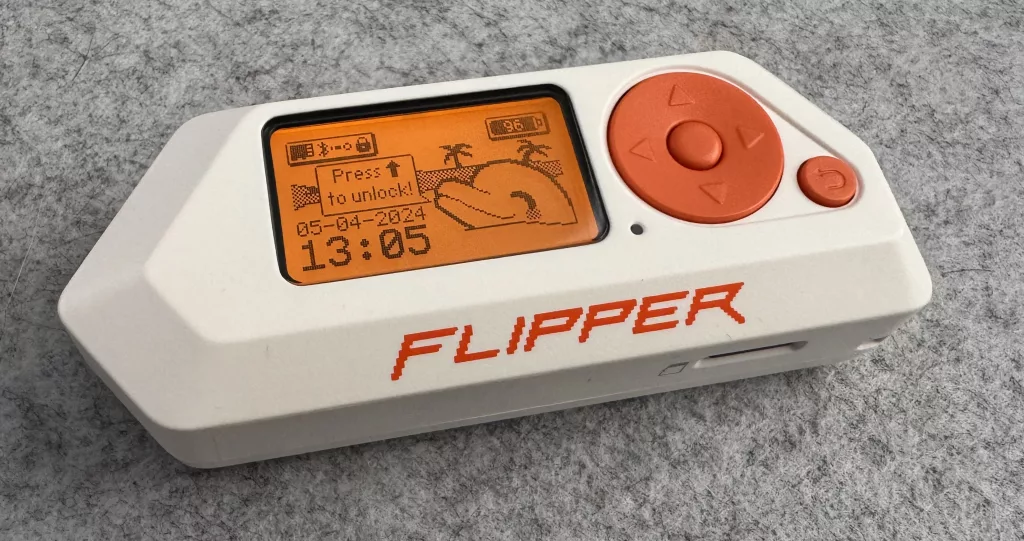
In recent years, the Flipper Zero has gained popularity among security enthusiasts and professionals for its versatility and ease of use, and I too love it.
This portable multi-tool for pentesters and tech enthusiasts allows users to interact with various digital systems and devices, including access control systems. One of its most appealing and useful features is the ability to clone access cards, making it a powerful tool for security assessments, and perhaps cloning your friends gate fob. However, while the Flipper Zero offers numerous capabilities, it’s essential to understand the risks associated with storing cloned access cards on the device. The primary concern is the lack of encryption for the data stored on its SD card.
Understanding the Flipper Zero
The Flipper Zero is designed to be a versatile tool for a variety of tasks, such as RFID and NFC emulation, infrared signal capture, and more. It’s compact, user-friendly, and can emulate different types of access cards used in various systems. This functionality makes it incredibly useful for penetration testers who need to demonstrate security vulnerabilities. However, this same functionality can pose significant security risks if not managed properly.
The risks of storing cloned access cards
1. Lack of data encryption
One of the most critical security weaknesses of the Flipper Zero is that the data stored on its SD card is not encrypted. This means that any sensitive information, including cloned access card data, is stored in plain text. If the device falls into the wrong hands, the stored data can be easily accessed and misused.
2. Physical theft
Given its compact size, the Flipper Zero is easy to carry around but also easy to lose or have stolen. If someone steals your Flipper Zero, they can access all the cloned access cards stored on the SD card without needing to bypass any encryption or security measures. This could potentially give unauthorised individuals access to secure areas.
3. Ease of data extraction
Since the data on the Flipper Zero’s SD card is not encrypted, anyone with basic technical knowledge can extract the card and read the data using a standard card reader. This simplicity in data extraction makes it a significant vulnerability.
4. Potential for unauthorised cloning
Storing cloned access cards on an unencrypted medium also opens the door for unauthorised duplication. If someone gains access to your Flipper Zero, they can copy the access card data and use it to create their own cloned cards, compromising security systems.
Best practices for using a Flipper Zero
To mitigate the risks associated with storing cloned access cards on a Flipper Zero, consider the following best practices:
1. Use secure storage alternatives
Avoid storing sensitive data on the Flipper Zero’s SD card. Instead, use more secure storage alternatives that offer encryption to protect your data.
Or, if you are pen testing, use what you find to document it, demonstrate it and then remove it.
2. Implement physical security measures
This isn’t something I’d find very practical , but for some, keeping your Flipper Zero in a lock box may work.
3. Don’t think the PIN is secure
Whilst the Flipper Zero does have a PIN feature, of sorts, and it may help keep a notive of your device, it does not protect the SD card. So be aware of this.
4. Educate users
If you are part of an organisation, educate users about the risks of storing sensitive information on portable devices like the Flipper Zero. Promote best practices for data security and device management.
Conclusion
While the Flipper Zero is a powerful and versatile tool for security professionals, it’s crucial to recognize and mitigate the risks associated with storing cloned access cards on the device. The lack of encryption for data stored on its SD card presents significant security vulnerabilities. By adopting secure storage practices, implementing physical security measures, and staying informed about potential risks, users can better protect their sensitive information and maintain robust security protocols.
Understanding these risks and taking proactive steps to secure your Flipper Zero can help prevent unauthorised access and protect your valuable data
Frequently answered questions
How can I encrypt the data stored on the Flipper Zero’s SD card?
You could encrypt the SD Card easily enough, but the Flipper Zero has so little memory, I don’t think it would handle it, even if the firmware was able to.
Are there any firmware or software updates planned to address these security vulnerabilities?
Regarding firmware or software updates, it is essential to regularly check the official Flipper Zero forums, GitHub repository, or the developer’s website for announcements on security updates and new features, so you always have the latest and greatest firmware, but I do not think you’ll ever overcome this.
However, if you use it responsibly, and don’t store sensitive data on there for long, if at all, then you’re minimising the risk.
What are the specific legal implications of using the Flipper Zero for cloning access cards?
As for the legal implications of using the Flipper Zero for cloning access cards, it is crucial to understand that unauthorised cloning or use of access credentials can be considered illegal in many country. I am not an expert on this, so even though I think it’s obviously illegal, if you are unsure I recommend you seek legal advise.

